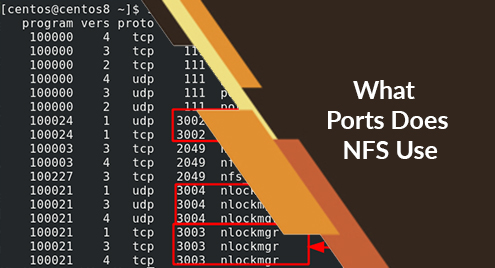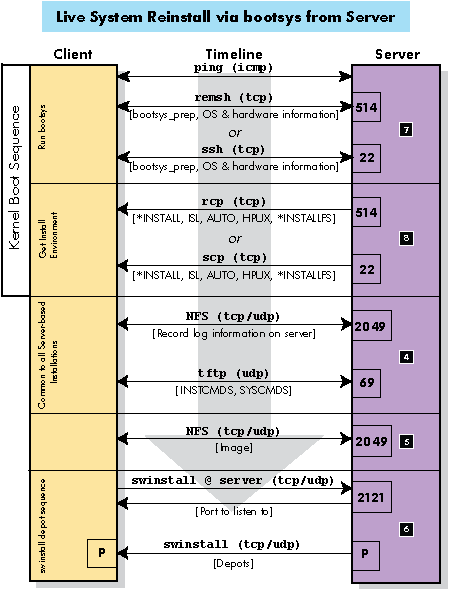
29.5 NFS Protocol | TCP/IP Illustrated, Vol. 1: The Protocols (Addison-Wesley Professional Computing Series)

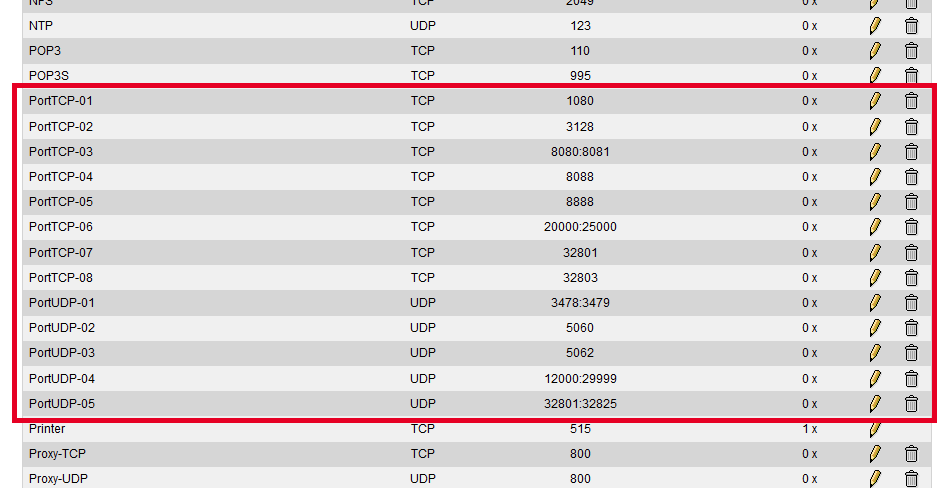
Network and Connectivity Requirements for PostgreSQL Environments - Documentation 5.0 - Delphix Documentation

Network and Connectivity Requirements for Oracle Environments - Documentation 5.0 - Delphix Documentation

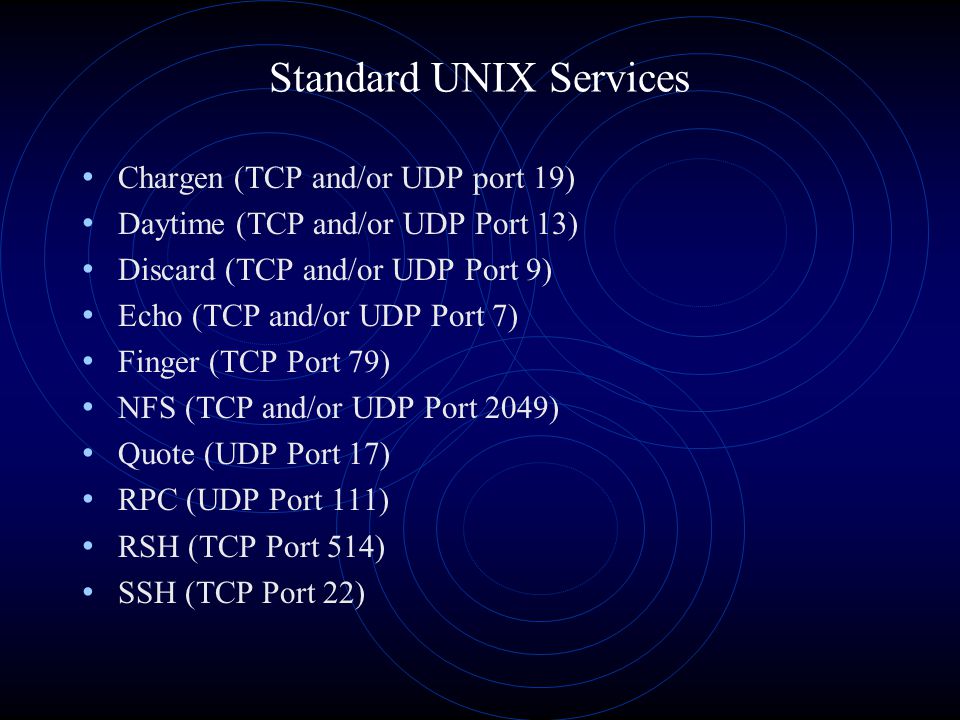
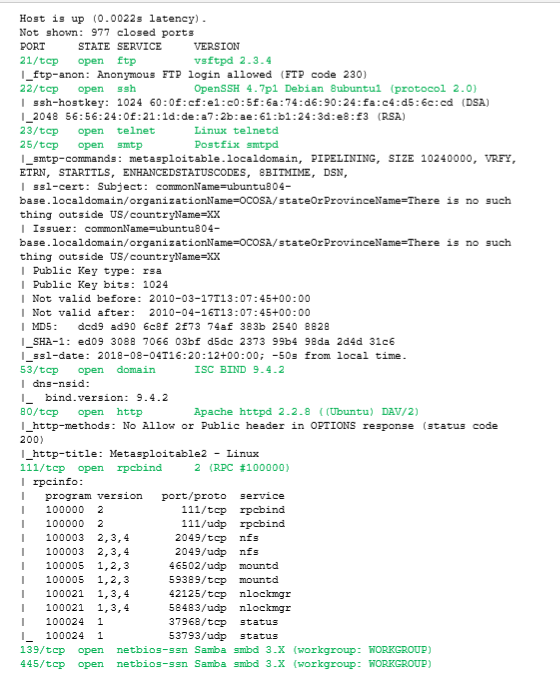
Interview #common #questions TCP/UDP port numbers. For cyber security professionals you can also think about the payloads you can use if these ports are open. #indincybersecuritysolutions #cybersecurity... - Indian Cyber Security Solutions -
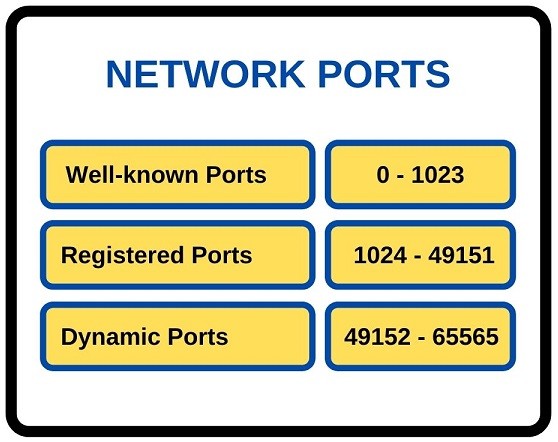
Preparing the Network for ThinLinc Installation — The ThinLinc Administrator's Guide 4.14.0 build 2408 documentation